FAQs: Globus Connect and Endpoints
- What are Globus Connect Personal and Globus Connect Server?
- What is an "endpoint"?
- How can I create an endpoint?
- Are transfers between Globus Connect Personal endpoints possible?
- How does Globus Connect Personal work?
- What can I do if my endpoint does not support timestamp preservation?
- Can I force encryption on an endpoint?
- Can I use a different PAM module for authenticating users to Globus Connect Server endpoint?
- How do I manage roles on my endpoint?
- What is the Console?
What are Globus Connect Personal and Globus Connect Server?
Globus Connect is easy-to-install, pre-configured software that turns your laptop, server, cluster or other local resource into a Globus endpoint.
There are two versions of Globus Connect, one for use with personal machines such as your laptop, and another for use with server-class machines such as campus computing clusters and lab servers.
Globus Connect Personal is used to create an endpoint on a single-user system, e.g. on a laptop or a personal desktop machine. We sometimes refer to this as a "personal endpoint". Use Globus Connect Personal to enable file transfer to and from your personal machine (laptop or desktop.) A Globus Connect Personal endpoint is intended to be used only by a single user.
Globus Connect Server is used to create an endpoint on a multi-user system, e.g. on a campus HPC cluster or a lab server. We sometimes refer to this as a "server endpoint". Globus Connect Server enables system administrators to turn shared resources such as campus clusters and lab servers into a Globus endpoint. If it is made publicly visible, a Globus Connect Server endpoint can be used by multiple Globus users.
What is an "endpoint"?
An "endpoint" is one of the two file transfer locations – either the source or the destination – between which files can move. Once a resource (server, cluster, storage system, laptop, or other system) is defined as an endpoint, it will be available to authorized users who can transfer files to or from this endpoint.
How can I create an endpoint?
If you wish to create an endpoint on a personal machine (laptop, personal desktop computer, etc.) please see the instructions for setting up a Globus Connect Personal endpoint here: Mac OS X, Windows, Linux.
If you are setting up an endpoint on a multi-user machine (e.g. HPC cluster, lab server, etc.) please follow the instructions in the Globus Connect Server Installation Guide.
Are transfers between Globus Connect Personal endpoints possible?
Yes. To transfer between two Globus Connect Personal (GCP) endpoints, one of the users must create a guest collection hosted on their GCP endpoint, then grant the other user(s) access to that collection. Any user that has access to that guest collection (via an individual permission or group permission ACL) can transfer between it and their GCP endpoint. To create a guest collection, the endpoint must be associated with a Globus subscription.
How does Globus Connect Personal work?
Globus Connect Personal communicates with the Globus service to receive the commands needed to perform and manage transfers. File data itself is always transferred directly between the Globus Connect Personal endpoint and the destination endpoint – data does not "flow through" Globus in any way.
What can I do if my endpoint does not support timestamp preservation?
In the event that you see an error like this - Message: This server version does not support timestamp preservation, follow the steps below.
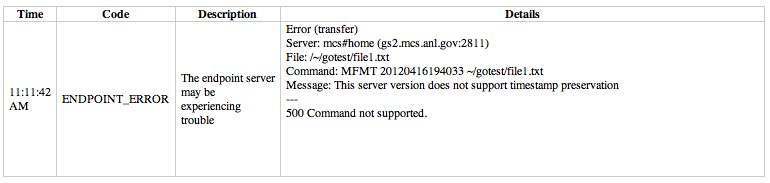
-
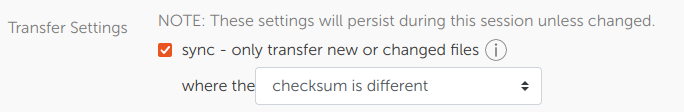
Cancel your job and restart it without the timestamp preservation option.
-
Also, restart with the 'Transfer & Timer Options' setting:
Can I force encryption on an endpoint?
Globus Connect Server Endpoint
For Globus Connect Server endpoints, the 'force encryption' option must be set per collection using the globus-connect-server collection create or update commands. For example:
$ globus-connect-server collection update --force-encryption $MY_COLLECTION_IDWhen the 'force encryption' option is set on a mapped collection, all guest collections backed by that mapped collection will also force encryption for transfers.
If a Globus Connect Server endpoint has High Assurance storage gateways, then all collections backed by those storage gateways will force encryption on all transfers.
Globus Connect Personal
The administrator of a Globus Connect Personal endpoint can force encryption for their endpoint in two different ways:
-
Look the endpoint up in the collections page in the Globus Web App, click the endpoint, click the 'edit attributes' button in the Overview tab, and then select 'yes' for the 'force encryption' option.
-
The administrator of the endpoint can use the endpoint modify command in the Command Line Interface (CLI) to force encryption. See documentation for the update command. Example:
$ globus endpoint update --force-encryption $MY_ENDPOINT_ID
When the 'force encryption' option is set on an endpoint, all shares hosted on that endpoint will also force encryption for transfers.
To only force encryption on specific collections on an endpoint, simply leave the 'force encryption' option set to 'no' for the endpoint itself, and then enable the 'force encryption' option for the particular collection(s) in question using the same two methods discussed above.
Can I use a different PAM module for authenticating users to Globus Connect Server endpoint?
The Globus OIDC server (which is an optional identity provider option for Globus Connect Server) will use the PAM login service by default, but can be configured to use a different PAM service if desired. We discuss how to configure the Globus OIDC server to use a different PAM service in our doc here.
How do I manage roles on my endpoint?
The Globus Web App provides an interface to manage roles on the endpoint on the Endpoints page. You can see a description of the supported roles here. Once you select your endpoint, you can choose the Roles tab to grant/revoke various roles on the endpoint.
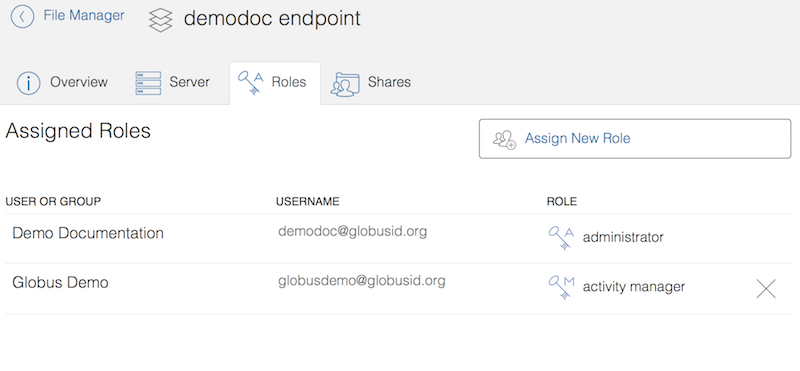
Note that your endpoint needs to be associated with a subscription to be able to set roles on the endpoint.
You can also use the Transfer API to manage roles on an endpoint.
What is the Console?
The Console provides a web interface for Administrators, Activity Managers, and Activity Monitors to monitor or manage activity on subscribed collections. It also allows Administrators to find and edit Globus Connect Server endpoints (subscribed or not).
The Dashboard tab includes an interactive, graphical representation of activity across all of your subscribed collections where green represents transfers that are making progress (or queued), orange represents transfers that are paused, and red represents tasks that are being retried because of errors. The Dashboard tab also includes a list of all your subscribed collections. Globus Connect Server endpoints do not appear on the Dashboard tab because they do not support data access. If you have a role on a mapped collection, you can view the activity of any guest collections by selecting the funnel icon of the mapped collection.
The Activity tab can be used to view and manage active tasks across all of your subscribed collections. Completed tasks may also be viewed in the Activity tab on a per collection basis. Tasks are visible for ninety days after completion and event logs are visible thirty days after task completion.