FAQs: Security
- Does Globus need credentials when accessing my system? Does it store these permanently?
- How does Globus ensure my data is secure?
- How does Globus use my Google account?
- How do I stop Globus from automatically authenticating using my Google account?
- Which method should I use to sign in to Globus?
- What authentication methods does Globus support for endpoint and collection access?
- Does Globus support one-time passwords (OTP)?
- How does Globus work with ACCESS security infrastructure?
- How can I delete my Globus account?
- Why am I sometimes asked to login again when accessing certain Globus collections?
- What is Globus ID?
- What is my Globus account?
- Why should I link identities?
- How do I get my organization added as an option to log into Globus?
Does Globus need credentials when accessing my system? Does it store these permanently?
Globus uses only temporary credentials to act on your behalf when making a transfer request, and never keeps your password nor long-term credentials to access a site.
How does Globus ensure my data is secure?
Globus uses a "data channel" for moving data between two endpoints. This data channel is established directly between the source and destination endpoints and cannot be accessed by Globus, only by the GridFTP servers running on the endpoints.
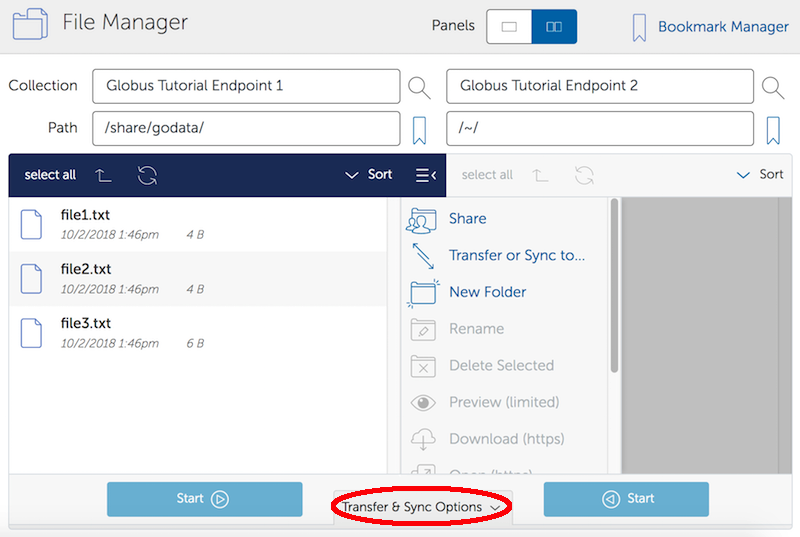
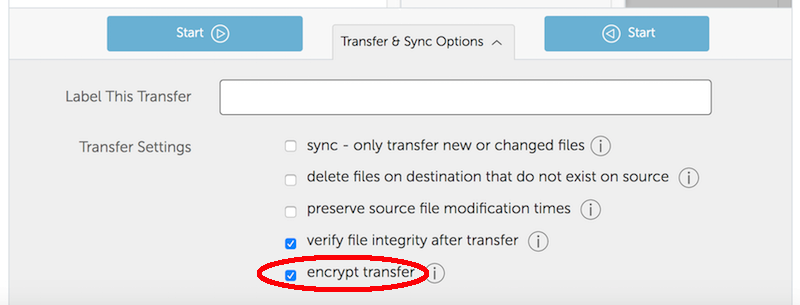
By default the data channel is authenticated, but unencrypted. It can be encrypted by selecting the "encrypt transfer" option on the File Manager page (see screenshot below), or by including the —encrypt option for the transfer command when using the command line interface. You should be aware that encryption adds processing overhead, and will likely reduce transfer speed. Encrypted transfers use the SSL cipher configured on the endpoints (the default for OpenSSL is AES256-SHA).
In addition to the data channel, Globus uses a "control channel" to communicate with the source and destination endpoints for a transfer. All control channel communications are encrypted.
How does Globus use my Google account?
You can use your Google identity to log into Globus. Select Google as an option from the organizations listed on the Globus login page, and sign in with your Google account. If you have previously logged into Globus using another identity (e.g. your campus username), Globus will give you the option to link it with your Google identity under a single Globus account. If you choose to link, you can use any of your linked identities to access Globus. You can choose not to link and keep your Google identity as a separate Globus account. You can manage your linked identities on the Globus Identities page.
How do I stop Globus from automatically authenticating using my Google account?
Visit this link on Google (you may be prompted to login using your Google account). You will see a list of websites for which you have authorized access to your Google account. Select the Globus entry and click the "Remove" button. Your Google account will no longer be used by Globus. If you try to login to Globus with your Google account, you will be asked to re-confirm that Globus may use your Google account.
Which method should I use to sign in to Globus?
You can use a username and password from any organization that is recognized (and trusted) by the Globus service. Select your preferred organization from the list on the Globus login page, and you will be redirected to your organization’s login page to provide your credentials. If you don’t see your organization listed or would like to create a separate account, you can use Google, ORDIC,or Globus ID to sign into Globus.
What authentication methods does Globus support for endpoint and collection access?
Please see our Globus Connect Server v5 Authorization and Authentication guide.
Does Globus support one-time passwords (OTP)?
Yes, one-time passwords work with Globus and do not require any specialized configuration. To access a site that requires an OTP, simply enter your password and token as you would normally when prompted by the site’s login page.
How does Globus work with ACCESS security infrastructure?
If you have an ACCESS account and you’ve been authorized to use an ACCESS resource, you can use Globus to access your storage on the ACCESS resource.
You can login to Globus using your ACCESS identity, or you can login to Globus using a different identity (e.g., your campus identity) and link your ACCESS identity. When you browse a collection on an ACCESS resource, Globus will ask you to authenticate using your ACCESS identity if you haven’t recently enough.
You’ll use the ACCESS InCommon login service to authenticate. Globus cannot see your ACCESS password when you enter it, but it receives your ACCESS username once you have successfully authenticated. This login is valid for a time period determined by the ACCESS resource administrator.
Once you’ve authenticated using your ACCESS identity, you can access your ACCESS storage just as you would any other Globus collection.
If you’re using the Globus command line interface (CLI) to access an ACCESS collection, the CLI will print a web address that you must open with a browser. You’ll perform the same ACCESS authentication process described above in your browser, then continue with the CLI.
How can I delete my Globus account?
Please complete the steps below and then send email to support@globus.org requesting that your account be deleted:
-
Remove yourself from all Globus groups.
-
Delete your Globus endpoints, including all shared endpoints that you created (note that users to whom you granted access to a shared endpoint will no longer be able to access the files on that endpoint).
-
Delete your Globus endpoint bookmarks.
-
Unlink any other accounts:
-
Go to your Identities page
-
Click on Manage Your Identities
-
Click X for each identity
-
-
Remove your consents:
-
Go to your Identities page
-
Click on Manage Your Consents
-
Click X for each consent
-
Why am I sometimes asked to login again when accessing certain Globus collections?
For high-assurance guest collections, users have to authenticate with the identity that grants them access within their current browser session for data access and managing permissions. For example, say a user had student-account@example.edu and personal-account@example.com as linked identities, and the data was shared with student-account@example.edu. If the user logged in to the application using personal-account@example.com, they would be prompted to authenticate with student-account@example.edu within the session for data access. The user will also be prompted to log in again with student-account@example.edu when the session timeout value configured on the collection has been reached.
What is Globus ID?
Globus ID provides and manages identities (usernames and passwords) for use with the Globus service. It is an independent service operated by the Globus team for those users that choose not to use their organization’s login to access Globus (and for users whose institutional identity provider is not yet supported by the Globus service). A Globus ID is not required to use Globus - you are encouraged to access the service using your institutional username and password.
What is my Globus account?
Your Globus account is the set of linked identities that you have used to log into Globus. Click here to see the set of identities for your Globus account.
Why should I link identities?
Globus allows users to link their many identities (e.g., university login, facility logins, Google, Globus ID) into a single Globus account. This allows the user to have a single account to manage their resources across these multiple identities. For example, a user with a University of Chicago account might also have an Argonne National Laboratory account. By linking those together into a single Globus account, use of services such as Globus Transfer and Groups using either identity is consolidated under that single Globus account.
How do I get my organization added as an option to log into Globus?
If your organization is part of the InCommon Federation, the administrator of your campus identity system can configure it to work with Globus. Globus supports logins from InCommon members whose identity systems release Research & Scholarship attributes.
Please send the following information to your IT administrator: "To setup your Identity Provider for use with Globus, please see this CILogon FAQ. If your identity provider is listed in CILogon, but not in Globus, please ensure that Research and Scholarship attributes are released to CILogon as described in the InCommon documentation. You can confirm that your institution is releasing Research and Scholarship attributes by visiting the InCommon organizations list and filtering to "Research & Scholarship Adopters". Once your organization’s system is configured to release the required attributes, it will appear in the list of institutions on the Globus login page within two business days and can be selected by your users."
It is required for an organization to release the full Research and Scholarship attribute bundle for that organization to be automatically detected and added as a Globus login option. It is also possible for organizations which have a Globus Subscription, and that release at least the ePPN and ePTID, to be added manually. In such a case, the organization will need to submit a request with Globus Support asking for this to be done.
If your organization is not part of the InCommon Federation, you can request to add your organizational login as an alternate identity provider in Globus. Your system must support the OpenID Connect protocol, and be registered with Globus as a trusted identity provider. Please submit this form so we can register your system. Once the request is vetted and approved, your identity provider will be available as an option for login.